环境
谷歌云vps、ubuntu18
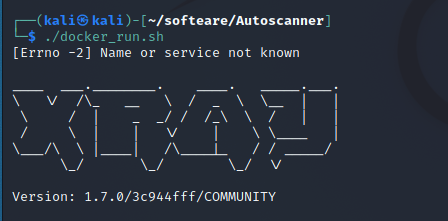
现象
1、oneforall跑完后,未看到xray在工作;/root/Autoscanner/tools/xray_linux_amd64目录下xray的证书信息、配置文件也不存在
2、Nuclei只跑完www.xxx.com的主域名,进程就结束了
3、日志信息
21:31:35,356 [INFOR] oneforall:253 - Finished OneForAll
Request Progress: 131it [00:42, 3.05it/s]
286
2022-03-18 21:31:35.478 | INFO | lib.Tools:__init__:56 - www.lenovo.com - Oneforall - over
2022-03-18 21:31:35.538 | INFO | lib.Tools:__init__:49 - www.lenovo.com - Bugscanner - start scanning
2022-03-18 21:31:36.613 | INFO | lib.Tools:__init__:56 - www.lenovo.com - Bugscanner - over
2022-03-18 21:31:36.614 | INFO | lib.Tools:__init__:49 - www.lenovo.com - Nslookup - start scanning
2022-03-18 21:31:42.482 | INFO | lib.Tools:__init__:56 - www.lenovo.com - Nslookup - over
2022-03-18 21:31:42.488 | INFO | lib.Tools:__init__:49 - 23.59.108.184 - Masscan - start scanning
Error in received packet: No such file or directory
src/rawsock-getif.c:299: read_netlink: 2
FAIL: could not determine default interface
FAIL:... try "--interface ethX"
311
2022-03-18 21:31:42.592 | INFO | lib.Tools:__init__:56 - 23.59.108.184 - Masscan - over
2022-03-18 21:31:42.593 | INFO | lib.Tools:__init__:49 - /tmp/tmpttz7zu0m - Nmap - start scanning
320
2022-03-18 21:31:59.095 | INFO | lib.Tools:__init__:56 - /tmp/tmpttz7zu0m - Nmap - over
/usr/lib/ruby/vendor_ruby/target.rb:188: warning: URI.escape is obsolete
/usr/lib/ruby/vendor_ruby/target.rb:188: warning: URI.escape is obsolete
/usr/lib/ruby/vendor_ruby/target.rb:188: warning: URI.escape is obsolete
2022-03-18 21:32:09.536 | INFO | lib.Tools:__init__:49 - 23.59.108.184 - IpLocation - start scanning
2022-03-18 21:32:09.615 | INFO | lib.Tools:__init__:56 - 23.59.108.184 - IpLocation - over
2022-03-18 21:32:09.616 | INFO | lib.Tools:__init__:49 - - Whatweb - start scanning
/usr/lib/ruby/vendor_ruby/target.rb:188: warning: URI.escape is obsolete
/usr/lib/ruby/vendor_ruby/target.rb:188: warning: URI.escape is obsolete
/usr/lib/ruby/vendor_ruby/target.rb:188: warning: URI.escape is obsolete
383
2022-03-18 21:32:18.629 | INFO | lib.Tools:__init__:56 - - Whatweb - over
2022-03-18 21:32:18.629 | INFO | lib.Tools:__init__:49 - http://www.lenovo.com:80 - Snapshot - start scanning
2022-03-18 21:32:25.103 | INFO | lib.Tools:__init__:56 - http://www.lenovo.com:80 - Snapshot - over
2022-03-18 21:32:25.103 | INFO | lib.Tools:__init__:49 - http://www.lenovo.com:80 - Nuclei - start scanning
__ _
____ __ _______/ /__ (_)
/ __ \/ / / / ___/ / _ \/ /
/ / / / /_/ / /__/ / __/ /
/_/ /_/\__,_/\___/_/\___/_/ 2.6.3
projectdiscovery.io
[WRN] Use with caution. You are responsible for your actions.
[WRN] Developers assume no liability and are not responsible for any misuse or damage.
[INF] nuclei-templates are not installed, installing...
[INF] Successfully downloaded nuclei-templates (v8.9.0) to /root/nuclei-templates. GoodLuck!
[INF] Using Nuclei Engine 2.6.3 (latest)
[INF] Using Nuclei Templates 8.9.0 (latest)
[INF] Templates added in last update: 2
[INF] Templates loaded for scan: 3013
[INF] Templates clustered: 502 (Reduced 461 HTTP Requests)
[INF] Using Interactsh Server: oast.me
485
2022-03-18 21:33:56.049 | INFO | lib.Tools:__init__:56 - http://www.lenovo.com:80 - Nuclei - over
2022-03-18 21:33:56.050 | INFO | lib.Tools:__init__:49 - http://www.lenovo.com:80 - Crawlergo - start scanning
724
2022-03-18 21:34:16.972 | INFO | lib.Tools:__init__:56 - http://www.lenovo.com:80 - Crawlergo - over
2022-03-18 21:34:32.018 | INFO | lib.Tools:__init__:49 - http://www.lenovo.com:80 - Dirsearch - start scanning
778
2022-03-18 21:35:19.327 | INFO | lib.Tools:__init__:56 - http://www.lenovo.com:80 - Dirsearch - over
root@instance-2:~/Autoscanner#